Imagine the sinking feeling you’d get if you checked your credit score, expecting to see your typical, healthy 730-ish, and instead it was bottomed out in the low 400s.
You’re confused. How did this happen? You thought you were safe. Now you’re realizing you weren’t as safe as you thought you were.
Identity theft is one of the fastest-growing categories of crime. According to the Federal Trade Commission’s Consumer Sentinel Network, there were roughly 1.4 million identity theft reports filed with the FTC in 2023. It’s estimated that about 33 percent of U.S. adults have experienced some form of identity theft — that’s one in three.
You’re likely already familiar with the term “identity theft,” but you might not have a complete grasp of its scope. When we say “identity theft,” what do we actually mean?
What Is Identity Theft?
Identity theft is a broad term that refers to using someone else’s personal information — like their name, driver’s license number, or credit card details — without their permission to commit fraud or other crimes.
Identity thieves gather this information in a variety of ways. It could be physically, by swiping your mail or going through your trash, or digitally, by hacking your network or purchasing your sensitive information on a dark web marketplace.
Regardless of how they get your information, fraudsters will use it to pose as you to make purchases, take out loans, or secure lines of credit. Identity theft can be tremendously costly, and can take years to recover from.
Did You Know? According to the FTC’s Consumer Sentinel Network report, identity theft victims who experienced monetary loss reported a median loss of roughly $500, though individual losses can reach into the thousands. To protect yourself, consider looking over our list of the best identity theft protection services for 2026.
Types of Identity Theft
This is by no means an exhaustive list, but it will give you a good idea of the many ways identity theft can occur. It’s not just maxing out your credit cards — there are types of identity theft that can be life-ruining.
Social Security Number Theft
Your social security number is the holy grail of your personal information. Once fraudsters have this, they can quickly use it to unlock your identity and wreak financial havoc, or sell it using online black markets to other bad actors for nefarious purposes.
Financial Identity Theft
This occurs when thieves gain possession of identifying financial information like your bank account numbers, retirement account numbers, investment account numbers, credit card numbers, or routing numbers. Once they have access to these items and perhaps a few more easily attainable pieces of information, they can access and drain your accounts. This can happen all at once, or slowly over time — just enough so you never realize it’s happening.
Tax Identity Theft
We wish this meant that some good-natured prankster would pay your taxes for you, but it’s actually the opposite. With a few pieces of identifying information, a thief can actually file your taxes early and claim your return as their own. According to the IRS, the agency identified approximately 1.1 million tax returns with confirmed identity theft in fiscal year 2023 alone. This type of identity theft isn’t extremely common, but it’s extremely hard to unravel and make right.
Medical ID Theft
This category is particularly nasty. Medical identity theft is when a criminal steals your personal information and uses your name, health insurance numbers, or Medicare number to submit insurance claims, file for prescription drugs, or even receive medical treatments themselves. If that wasn’t bad enough, this type of fraud could prevent you from being covered if you become sick, if the criminal caused you to reach your benefit limits. There are a few services out there that protect against medical ID theft.
Mail Identity Theft
Ah yes, the old-school way to steal an identity. This is how it was done in the years before the internet. Think about how much of your identifying information appears in your bills, your bank statements, and your insurance forms. And think about how those items usually are sitting in an unsecured box right in front of your house. How easy would it be for someone walking by to grab a fist full of your mail and use the information they found there to start accessing your personal and financial life?
Did You Know? The most common items stolen from mailboxes by identity thieves are bank statements, bills, and medical paperwork.
Digital Identity Theft
This is a pretty huge category, and could actually lead to any of the other types of identity thefts in this list. Digital identity theft occurs when a bad actor uses some sort of hacking, social engineering, or a combination of the two to either gain direct access to whatever target they have (like a bank account) or to glean enough personal information about you to set the stage for another type of attack.
ID Theft to Commit Other Crime
Some bad actors use identity theft as a secondary protection to their primary criminal enterprise. If they get caught by police performing whatever nefarious activities they engage in — it wasn’t them that did it, it was you. And they have the necessary identification to prove it. They make bail, skip town, and suddenly you get pulled over for rolling through a stop sign and get arrested for the crime they committed in your name. We’re not saying this will happen to you, but it’s something to be aware of.
Home Title Fraud
Did you know it’s possible for an identity thief to steal your house? While it’s pretty unlikely, it’s not unheard of. Determined fraudsters can actually gather enough information to pose as you, and then transfer the title of your home to themselves or another shell identity. They then use your home to take out equity loans or, if they can sell it outright, making off with the profits. Can you imagine the mess that would cause?
We don’t say all this to scare you, but we do want to make it clear that identity theft is a serious threat, and it’s not something you should take lightly. That said, there are certain folks who should be more concerned than others.
Who is at Risk of Identity Theft?
Unfortunately, the short answer is “everyone,” but there are a few population groups that are particularly vulnerable.
Prior Victims of Identity Theft
As terrible as it might be, people who have previously become victims of identity theft are at much higher risk of becoming targets again. The Center for Victim Research found that 7 to 10 percent of the population in the United States are victims of identity theft each year, and about 21 percent of those individuals have been victims before.
The Elderly
Senior citizens remain a favorite target of identity thieves because they tend to be more susceptible to social engineering. The most common attack vectors are phone scams and phishing emails. According to the FBI’s 2024 Internet Crime Report, adults over 60 lost more than $4.8 billion to fraud and cybercrime — more than any other age group. Those most at risk are elderly individuals whose cognitive abilities may be declining and who can be more easily confused or misled.
Children and Minors
Children are another prime victim of identity theft. Although you might think children are low risk because they do not yet have established financial lives, you’d be surprised. A child’s social security number can be used by fraudsters to apply for government benefits, open lines of credit, and take out loans. One of the most common ways for a child’s identity to be stolen, according to the federal trade commission, is through unsecured school records. To protect your child, ask how and where their information is being stored, or check out our guide on the highest-rated identity theft protection services for families.
The Deceased
Yes, even after death you can still have your identity stolen. The recently deceased are favorite targets for fraudsters, with 2.5 million deceased identities stolen every year in the U.S. Information is gleaned from public obituaries and the departed’s social security number is usually lifted from the Social Security Administrations Master Death File. Similar to the theft of a child’s identity, this type of identity theft can often go unnoticed for months or even years. There are a few services out there, though, that specialize in protecting the recently deceased.
Did You Know? It’s estimated that approximately 2.5 million deceased individuals have their identities stolen every year.
The Negligent
This is a pretty broad category, but hear us out. Those who are the most likely to become the victim of identity theft are those who are ignorant of the threats, those who aren’t vigilant about online privacy, and those who do little to protect their sensitive information. Identity thieves will always go for the easy targets, so it’s in your best interest to find ways to make sure you’re not the low-hanging fruit.
The good news is, protecting yourself from identity theft doesn’t have to be complicated. How can you protect yourself? We’ll show you.
Identity Theft Risks and How to Protect Yourself
Identity thieves will use any and all attack vectors, so it pays to shore up your defenses on all fronts.
Stolen Electronics
Nowadays our entire lives are in our phones and on our laptops. If either is ever misplaced or stolen, don’t take it lightly. Odds are it was lifted and pawned to make a few bucks, but your electronics could have ended up in the hands of a far more sophisticated thief who, using the information they found on your device, will slowly start piecing together enough information to gain access to your life. If your phone or laptop ever goes missing, contact your financial institutions, change your passwords, and lock down your accounts. It might seem like overkill, but trust us, if you do the work on the front end, you’ll be saving yourself a lot of ongoing grief.
Stolen Financial Information
An identity thief can get their hands on your financial information in a variety of ways — both digital and physical. Always watch your account diligently for charges you don’t recognize, and keep an eye on retirement and investment accounts. We’ll go into a little more detail on this later, but you always want to practice safe browsing habits online and generate strong passwords with two-factor authentication where possible.
Also, dispose of any documents with identifying information on them properly, and always check your mail promptly. And this should go without saying, but keep an eye on your wallet or handbag. You’re more than likely carrying around more than what a fraudster would need to steal your identity in your back pocket or pocketbook every day.
That said, criminals don’t always have to physically take your wallet — all they need are your credit and debit card numbers to access your accounts. If your card uses an RFID chip, criminals can use a device called an RFID skimmer to quietly harvest your card data without ever touching you. It’s essentially digital pickpocketing, and you’d never know it happened. To cut down your risk, consider investing in an RFID-blocking wallet or purse.
Did You Know? Radio-frequency identification, RFID for short, uses electromagnetic fields to identify and track objects. These objects probably include your credit and debit cards.
Digital Attacks
When you think of hacking you probably picture a guy surrounded by monitors running Matrix code for hours then suddenly exclaiming “I’m in!” In reality, it’s usually much different — and much simpler.
Yes, there are folks with the skills to break into your network using the equivalent of digital lock picks, but most of the time a hacker will use simple social engineering to have you open the door for them. Most of the time this comes in the form of “phishing” attacks, where an online fraudster will try to gain access to your account by posing as the institution, asking for your password on some bogus pretense. For example, if you receive an email from Apple asking you to confirm your password, it’s not from Apple. A good rule of thumb is that if you’re ever asked to provide sensitive information online, check with the institution before providing your info.
So that prevents the door-busters, but what about the lock-pickers we mentioned? To keep them out, invest in solid network protection. This means firewalls, antivirus software, and a good VPN.
Did You Know? VPN stands for virtual private network. To understand how they work, consider a car getting on the highway. The car is your data, and the highway is the Internet. Typical connections get you to the highway using surface streets, where it would be easy to get car-jacked. VPNs get you to the highway via a secured tunnel only you’re allowed to drive in.
Data Breaches
The term “data breach” is in the news a lot, but what is a data breach and how do they relate to identity theft?
Simply put, a data breach occurs when an organization exposes secure or confidential information to an untrusted environment. This could be a company’s records of their customers’ names and payment information, or a hospital’s catalog of patients’ medical identification and Social Security numbers. Breaches are usually caused by hackers seeking personally identifying information — also called PII — to sell as commodities on dark web marketplaces.
Once your information ends up there, identity thieves usually purchase entire databases of PII and test the information that works and the information that doesn’t. This is why it’s so important to be discerning about who you do business with online. Small, disorganized companies aren’t likely to have robust cybersecurity infrastructure in place and might fall victim to hackers more easily than a larger, more reputable source.
Data breaches happen in several ways. Hackers might exploit vulnerabilities in outdated security software to sneak malware into a company’s network and steal data. Or it could be something as simple as a weak password or a successful phishing attempt — if an employee is tricked into handing over their login credentials, that alone can trigger a full-blown breach.
Did You Know? A social engineering strategy where a hacker poses as a legitimate entity and requests PII or login credentials is also called a phishing attack.
Data breaches are a fact of modern life — and they’re expensive. In 2024, the average cost of a data breach hit a record high of $4.88 million for organizations. But for the individuals caught up in those breaches, the damage can be much harder to put a dollar sign on.
That’s why it pays to be vigilant when it comes to protecting yourself from data breaches. Be selective about who you choose to do business with. If an online vendor feels a little questionable, trust your gut. Use strong, secure passwords on all your accounts, and invest in antivirus software.
Did You Know? One way to tell if a website might be insecure is by looking at the URL address bar. Reputable sites use https protocol. If the “s” is missing, don’t enter your sensitive information on the site.
It’s also advisable to keep an eye on the news. Large-scale data breaches are widely reported. If you’ve done business with a company in the past that has been compromised, change your passwords, and watch your accounts. You never know who might have their hands on what in terms of your data.
Malicious Websites
Not every vendor online is acting in good faith, so be careful where you share your credit card information. You should also be discerning about where you get your entertainment. Many of the less-than-reputable streaming sites are lousy with malware that can infect your computer and cause untold damage.
Did You Know? Malware and Spyware are two different things. Malware is any software designed to damage a computer, server, client, or computer network. Spyware, on the other hand, is designed to gather information and send it back to a malicious entity.
What Are the Best Identity Theft Protection Services?
- Identity Guard
- IdentityForce
- LifeLock
- NordStellar
- CompleteID
- IdentityIQ
- Protection One
- Experian IdentityWorks
- Zander
- AllClear ID
- Trusted ID / Equifax
- MyIDCare
- ProtectMyID
- USAA
- Discover
- Chase
- Wells Fargo
Possible Warning Signs of Identity Theft
One of the reasons identity theft is so insidious is that it’s often exceedingly difficult to detect. However, there are some early warning signs that you’ve become the victim of identity theft. Let’s have a look.
Credit Score Fluctuations
Our credit scores change over time — that’s to be expected. It’s also to be expected that each of the three main reporting bureaus won’t have the exact same score. However, you should pay close attention to changes in your credit scores. Obviously huge, unexpected declines are a major red flag for identity theft, but that’s not always how identity theft presents itself.
Sometimes small fluctuations can indicate a credit inquiry has been made in your name. Maybe a single, low-limit credit card has been taken out in your name. Maybe an identity thief is poking around for vulnerabilities.
It’s a good idea to keep an eye on your credit scores. You can do this on your own by contacting the bureaus annually and asking for your report, or you can employ a service to do it automatically. If you’re more inclined to the latter, we’ve compiled a list of the best identity theft services for credit monitoring.
“Test” Charges on Accounts
Oftentimes, fraudsters purchase credit card information in bulk on the dark web with a “buyer beware” understanding that some of the accounts might work, some might not. To identify those that do, scammers will make small “test” purchases on the accounts. The scammer knows those that go through will work. If you see, say, a 99 cent charge on your credit card to a vendor you don’t recognize, do not shrug it off. This might indicate that a much larger purchase is coming on its heels.
Mail Irregularities
Were you expecting a bill that never showed up? Did you get a bill for a person you don’t recognize? Again, don’t shrug it off. Mail is still a primary vector of attack for identity thieves. If something is confusing or out of the ordinary, don’t just assume it was a fluke. Take a few minutes to follow up and figure it out, as the consequences could cost you more than you’ve bargained for.
Unexpected Account Entry Alerts
First of all — set up two-factor authentication wherever you can. If you’re unfamiliar with the concept, two-factor authentication is where a secure service requires two forms of proof that you are who you say you are. Say you want to log into your bank account from your desktop computer. When you enter your password, the bank sends you a text message with a code to enter. Once you input the code, you have access to your account. That’s two-factor authentication.
Now, if you receive an alert that the authentication has failed when you weren’t even trying to access the service or institution, that is almost always an indication that someone is trying to break in. Contact the issuing service immediately to let them know, and change your password. While we’re on the subject, please don’t use something simple like 1-2-3-4 as your password. Pick something stronger.
FYI: Strong passwords should be at least 8 characters long, and include a mix of upper- and lower-case letters, numbers, and special symbols. Avoid common words and phrases if you can. The strongest passwords are totally random.
Unexpected Healthcare Solicitations
Similar to what we said in the mail section, don’t ignore health solicitations that seem out of place. As innocent as it sounds, if you’re getting mail advertising a new blood pressure medication when you’re not suffering from high blood pressure, it might indicate you’ve become the victim of medical identity theft. Contact your healthcare provider to make sure no one has made claims in your name.
So let’s say one of the above scenarios happens to you. You do the right thing and look into it, but the worst is confirmed. You’ve become the victim of Identity theft. What do you do now?
What to Do if You’re the Victim of Identity Theft
Once you realize you’ve become the victim of identity theft, every second counts. You need to act fast to minimize the impact. We recommend you take the following actions…
Change Passwords
The first thing you should do is immediately change all of your passwords. If your identity has been compromised, there’s no telling what the thief has access to. Change your passwords to everything — yes, even your Netflix account. Identity thieves will use any foothold they can to break in.
Pro Tip: Never use the same password across platforms. Each password you use should be unique to the service it’s for.
Place Fraud Alerts
Once you place a fraud alert on your account, the credit bureaus are required to doubly scrutinize any requested access to your file. Contact them, explain the situation, and follow the steps required to place a fraud alert on your report. Once you contact one bureau, they are obligated to contact the other two. That said, you’ll still want to confirm that’s done. Here is the contact information for each bureau.
Credit Bureau Fraud Contact Information
| Bureau | Website | Phone Number |
|---|---|---|
| Experian | Experian Fraud | (888) 397-3742 |
| TransUnion | TransUnion Fraud | (800) 680-7298 |
| Equifax | Equifax Fraud | (888) 836-6351 |
Contact Your Financial Institutions
Next, you’ll want to let your financial institutions know what happened. Contact them, and they’ll direct you to their fraud division which will ask you for the details of your case, and suggest the actions you should take for mitigating the impact and managing remediation.
Contact the Organization Where the Fraud Occurred
If you fall victim to ID theft due to a data breach, for instance, immediately contact the organization or company that was breached. You’ll want to dispute charges made in your name or accounts opened on your behalf. They, too, will likely have a fraud division who can direct you based on your specific circumstance.
Report it to the Federal Trade Commission (FTC)
This next step is critical because it secures certain protections for you as the victim of identity theft. Visit the FTC’s identity theft portal, where you will start the process. You’ll speak with someone and give them as much information as possible, and they will help you develop a personalized recovery plan.
Once you’ve filed a report with the FTC, request a copy of it. Then, after you’ve collected your copy, you’ll go on to the next step.
Report the Incident to Police
With the FTC’s report in hand, contact your local police department to report the incident. You’ll likely be asked for your ID, proof of residence, and any evidence of the crime including fraudulent bills, credit report discrepancies, or IRS notices. The police will also provide you with a report which you’ll need for your ongoing recovery.
How To Report Fraud
There are multiple different types of fraud you might fall victim to, and just as many responses to make things right again. We’re going to go through the most common types of fraud and give you some quick walkthroughs on how to report it. But keep in mind that your situation is unique, so your response may need to be unique as well.
Reporting Identity Theft
Identity theft is one of the most common types of fraud out there, but it’s a pretty all-encompassing term. It could mean anything from someone physically using your credit card at a store for an unauthorized purchase, to someone using your personal information to transfer the title of your home into their name. No matter what, though, your starting point for reporting is going to be the Federal Trade Commission. They have an online portal for reporting identity theft where you’ll be able to tell them what happened and get a personalized recovery plan.
Reporting Social Security Number (SSN) Fraud
This is a specific type of identity theft where a fraudster uses another person’s social security number to collect their government benefits. This is typically a form of identity fraud against the elderly, against children, or against the deceased (believe it or not). If you suspect you or someone you care for has become the victim of SSN Fraud, contact the Office of the Inspector General at 1-800-269-0271. You can also submit a report using their online portal.
Did You Know? You don’t have to become a victim to report a scam. If you receive correspondence you believe is an attempt to obtain your social security number for nefarious reasons, get in touch with the Office of the Inspector General.
Reporting Credit Card Fraud
Credit card fraud is extremely common and can be accomplished in a variety of ways by scammers. They might purchase your information on the dark web, they might go through your mail to get your account numbers, or they might use some form of social engineering to gain access to your accounts. Regardless, you’ll want to take care of this fraud decisively.
The good news is most credit card issuers offer zero fraud liability on unauthorized charges, but you’ll still need to stop the charges before you can use this protection. Contact the issuer — if they haven’t contacted you first — and tell them the situation. Depending on the severity and complexity of the situation, they might do anything from issuing you a new card to closing an existing account. Regardless, you should change all your banking passwords just to be safe.
FYI: According to the Fair Credit Billing Act, you need to report fraudulent charges within 60 days of receiving your billing statement that contains the suspicious activity. Beyond that deadline, you might become responsible for the debt.
Don’t worry about your credit report if the charges haven’t been sent to collections. You’re only going to get dinged if your credit card issuer doesn’t know about the fraudulent activity and it goes unpaid. You might consider placing a credit freeze at the three bureaus, though, to prevent a fraudster from taking out new lines of credit in your name.
How to Recover from Identity Theft
Recovering from identity theft is an arduous process that can take months or years, depending on the severity of the incident. Despite this sobering fact, there are steps to take and an order to the processes. Here are a few important considerations to help you recover from identity theft.
Close Fraudulent Accounts
First, you’ll need to identify the fraudulent accounts made in your name. Depending on how your identity was stolen, this might be a simple or complex task. With your police report and FTC report, contact agencies where accounts were opened or lines of credit issued. Request written documentation that the fraudulent account isn’t yours, and that you are not liable for the debt. Also request proof that they have removed any fraudulent debt from your credit report. Keep track of all correspondence for your records.
Pro Tip: Make sure to write down the date, time, and name of the person or people you spoke with. This will help you keep track of everything during a stressful, complicated time.
Dispute Fraudulent Charges
Locate the contact information for the dispute resolution of every business whenever fraudulent money was spent and ask if they will accept the identity theft report provided to you by the FTC as proof of the incident. If they won’t, that usually means they have their own protocols. Work with them and their processes to get the charges removed.
Make sure to follow up to receive a confirmation letter that states the fraudulent information has been removed. Save this information in case more fraudulent charges appear in the future.
Correct Credit Reports
Now that you have all your fraudulent use resolution letters from the businesses where your information was used, you will need to write to all three credit bureaus to have corrections made to your credit reports.
For this, you will need a copy of your dispute resolution letters from the businesses involved, as well as the Identity Theft Report from the FTC. You will also need to provide proof of your identity, such as your driver’s license or state-issued ID. You’ll need to explain what happened, indicate which entries are the fraudulent accounts involved in the incident, then ask them to block that information from your credit report.
Here’s where you’ll mail your information.
Credit Bureau Fraud Department Mailing Addresses
| Credit Bureau | Address |
|---|---|
| Experian | P.O. Box 9554 Allen, TX 75013 |
| TransUnion | P.O. Box 2000 Chester, PA 19016-2000 |
| Equifax | P.O. Box 740256 Atlanta, GA 30374-0256 |
If your identity is stolen, you have the legal right to have the fraudulent information removed from your credit reports; however, you will have to follow the proper steps in proving that identity theft occurred. Once you do, the credit bureaus will block the information from your reports and the affected companies cannot attempt to collect that debt. The credit bureaus can’t refuse your request to have the information blocked as long as you have the corresponding Identity Theft Report from the FTC.
That said, you can still request the fraudulent information be blocked from your credit reports even if you don’t have that report from the FTC, but there’s no guarantee they will honor your request.
Vigilantly Monitor
The best way to avoid becoming the victim of identity theft again is to continue monitoring your personal information and all three credit reports regularly. All three credit bureaus will provide you with one free credit report annually, but you’ll want to monitor it more closely than that — at least once per quarter. These additional copies will cost a little bit of money, but the peace of mind you’ll get when nothing unexpected shows up is priceless
You can call to get your free credit report from each of the credit bureaus below.
Credit Bureau Phone Numbers
| Credit Bureau | Phone Number |
|---|---|
| TransUnion | (800) 916-8800 |
| Equifax | (888) 378-4329 |
| Experian | (877) 322-8228 |
This might sound like a lot to think about. But unfortunately, it’s what millions of Americans have to deal with every year. Fortunately, many identity theft protection services offer robust recovery options.
Tips for Identity Theft Prevention
There are several things you can do to mitigate the risk of becoming the victim of identity theft. Here are our top recommendations to safeguard your identity and finances.
Keep Identification Secure
Keep important documents under lock and key. This means your passport, your social security card, and your medical ID should be in a safe unless you’re using them. Really, you should leave the majority of your credit cards at home unless you’re using them, too. It’s likely that in your wallet right now is enough information to steal your identity in half a dozen different ways; only carry around the items you need for the day.
Increase Situational Awareness
While it might seem like identity theft happens out in the ether, there are very real physical signs that it might be occurring. Is someone following you too closely? Is someone looking over your shoulder when you’re entering your PIN at the ATM? Did someone bump into you oddly? Did you receive a suspicious email? These can all be indications that a person is trying to steal your identity.
Pro Tip: Your cellphone is probably the single biggest distraction to situational awareness. When you’re out in public, keep your phone tucked away in your pocket and keep your head up.
Watch Out for Social Engineering Scams
Did you just receive a weird call from someone asking you to confirm your credit card number? Instead of talking with the person, hang up and call the asking agency back, requesting confirmation that the request was legitimate. A strange email asking for your password? Do the same. Scammers prey on the average person’s willingness to trust them. We’re not saying you need to put on the tinfoil hat to keep people from reading your brainwaves, but approach each situation with a healthy dose of caution.
Never Use Unsecured WiFi Networks
It’s nice to go to the coffee shop with your laptop on occasion to do some light work or web browsing, but you don’t know who else might be on the coffeeshop.guest. Network. If you want to engage in this type of activity, make sure you’re running a VPN, and you’re not accessing sensitive information like your bank account or purchasing anything online.
Pick Up Mail Immediately
We’ve touched on this previously, but you should know when your letter carrier is coming and plan to pick up your mail shortly thereafter. You don’t need to be waiting at the mailbox, but you don’t want your correspondence sitting there for too long — particularly when you’re expecting an important item like a new credit card or a medical bill.
Review Your Bank Accounts Daily
You should make it part of your daily routine to check your accounts for fraudulent activity. Wake up, wash your face, brush your teeth, check your banking app. This doesn’t need to be a full-blown forensic accounting investigation every day — just a simple once over to make sure there’s nothing showing up that’s unexpected. You should also review your credit report from each bureau once a year, just to make sure there are no discrepancies.
Did You Know? According to the FTC, one in five people has a mistake on their credit report.
Invest in a Shredder
Physical identity thieves love trash almost as much as they love mail. How often do you throw away credit card statements, old bills, and medical receipts? These documents are a treasure trove for identity thieves. Before you trash it, make sure it’s unrecognizable.
Secure Yourself Digitally
We’ve touched on this already, but it bears repeating. If you want to protect your identity, you absolutely must practice good online habits. Don’t visit unscrupulous websites, and be very careful where you enter your personal information. Make sure all of your software is up-to-date, and consider utilizing secondary security measures like antivirus software and a VPN.
Place a Credit Lock
This might be the single most important way you can protect yourself from Identity theft. A credit lock blocks access to your credit report, making it a lot harder for identity thieves to take out lines of credit or loans in your name. A credit lock accomplishes the same thing as a credit freeze, but it’s easier to set up and remove.
Get a Good Identity Theft Protection Service
Identity theft protection services, for the most part, alert you quickly if something is out of place or looks suspicious. They also make it easy to monitor your finances and personal data to make sure they’re safe. Plus, some of them even provide access to extra security tools, like an antivirus or a password manager.
We’ll discuss what kind of features you get with top identity theft protection services in the next section, and also show you how to pick the right service for you.
Common Features You’ll See Offered by Identity Theft Protection Services
Social Security Number Monitoring
This function scans public records and other databases for instances of your social security number being used. If it’s being used in association with something you don’t recognize, odds are your identity has been compromised.
Dark Web Monitoring
The “dark web” is a large subsection of the internet that is unindexed — meaning you can’t find its pages using regular search engines — and obfuscated — meaning its sites are purposefully hidden and only accessible using certain software. This is where the vast majority of the identifying items stolen in an identity theft event are traded as commodities. Dark Web Monitoring scans these black markets for your information and will alert you if it shows up where it shouldn’t.
We saw some of the best dark web monitoring features we’ve ever encountered when we reviewed Identity Guard. If this is something important to you — and it should be — consider checking them out. We’ve also written up an Identity Guard plans and pricing guide so that you can read more about this brand, which happens to rank as the most comprehensive protection available.
Did You Know? The internet is divided into two sections — the surface web and the deep web (of which the dark web is a small subset.) The surface web — which is what we use in our day-to-day lives — is only a tiny part of the internet as a whole. It’s estimated that the deep web is 400 to 500 times larger than the surface web!
Credit Monitoring
This is a critically important function for any identity theft service. This service will monitor your credit score or scores for you and alert you if there are any suspicious changes.
Address Change Monitoring
One tell-tale sign of identity theft is the spoofing of a new real or fictitious address using your name. This function scans the USPS databases for change of address forms using your information.
Court Record Monitoring
If a crime is committed in your name, court record monitoring will let you know about it. This is important for keeping your reputation from being tarnished, or ending up in the slammer yourself.
Financial Account Monitoring
With this functionality, you’ll be able to set thresholds for how much money can move out of or between your accounts. If anything happens beyond the threshold, you’ll immediately know. Remember, if you become the victim of identity theft, time is of the essence.
Bank Account Takeover Monitoring
This happens when an unauthorized person takes over, or gains access to your account directly. Once in the account, the bad actor can send money out to a new payee, or, if they are amateurs, purchase items directly. Takeover monitoring watches for this and alerts you if you’re at risk.
There are myriad other services offered by identity theft protection companies including social media monitoring, home title monitoring, sex offender monitoring, and even payday loan monitoring. Selecting the right service for yourself can seem overwhelming, but don’t worry — we’ve got you covered.
What to Look for When Selecting an Identity Theft Protection Service
First and foremost, you need to get a priority list together based on your daily habits and concerns.
Do you do a lot of online shopping and browsing? You might want to look for a service with robust dark web scanning. Consider checking out our guide about IDX — they do a great job of that.
Do you have a pretty complicated financial situation? You might consider a service that prioritizes credit monitoring and reporting, like we found when we reviewed Experian IdentityWorks.
Do you want to protect a large family without breaking the bank? Check out our Aura review, as they have budget-friendly family plans.
That said, there are always a few items we recommend when selecting a service. First, you should always look for a product that will monitor all three credit bureaus — Equifax, TransUnion, and Experian. The different bureaus monitor similar items, but each uses different evaluation processes, meaning that something that will immediately show up in one report might not in the other two. You should err on the side of caution here and go with a service that keeps an eye on all three.
You’ll also want a service that monitors your identity completely. What you consider “complete,” is up to you, but at a bare minimum, we’d look for a service that monitors your bank accounts, your social security number, your address, your driver’s license number, your passport number, your credit and debit cards, and your medical ID. Here’s an example of what LifeLock covers, for some context.
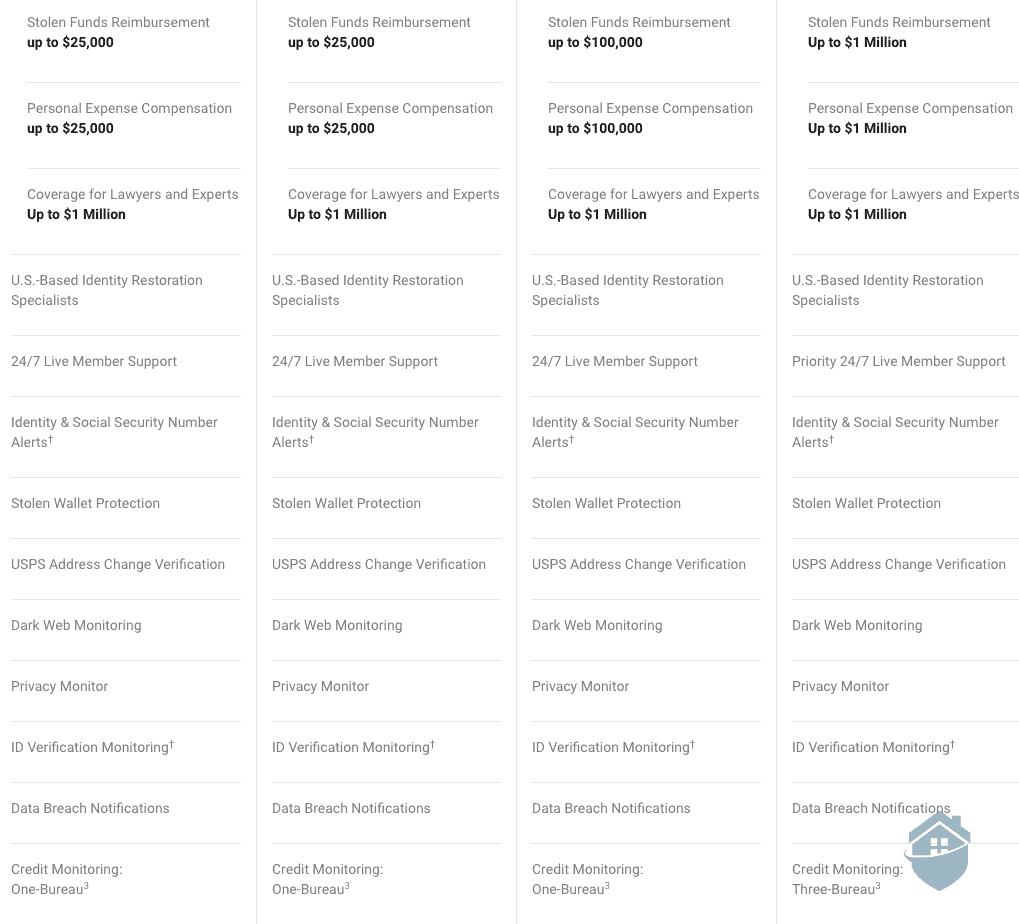
LifeLock Plan Features
If you want to learn more about this brand, we suggest reading our review of LifeLock. They have some pretty impressive device protections to safeguard your digital identity, on top of identity protections. You can also look into our guide to LifeLock’s plans and pricing to find a tier of service that would be right for you.
Also, invest in a service that has robust dark web monitoring with data breach alert functionality. Identity theft is increasingly taking place in digital spaces, so you’re going to want a service that’s focused on these marketplaces.
Finally, consider your budget. While there are, of course, outliers, generally speaking, a decent identity theft protection service will cost you anywhere between $10 and $30 per month. More than worth it, in our opinion, to protect yourself from what could be potential financial ruin.
It’s a lot to consider, for sure, but luckily we’ve built a tool to help you compare different identity theft services, and see which one is right for you.
Additional Identity Theft Resources
If you do not have an identity theft protection service and are concerned you may be a victim of identity theft, here’s a list of resources where you can find the information you need to get back on your feet.